How to restrict openvpn clients to communicate with other vpn clients
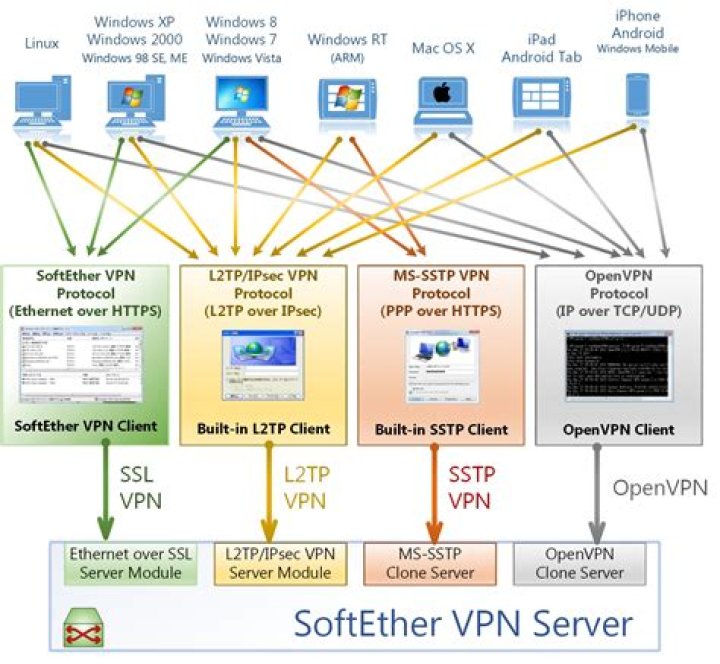
I have this Openvpn scenario..
I have Lot of openvpn clients connected to my server, All i want is to restrict client to client communication.
for eg. i have (10.20.0.2,10.20.0.3,10.20.0.4,10.20.0.5) clients 10.20.0.2 should not talk to 10.20.0.3 or 4, 5
Is there any way to achieve this using iptables? or through editing Configuration file?
12 Answers
Stan,
gertvdijk is only partially correct. What you must do is disable client-to-client in the server configuration file, but you also must configure OpenVPN in a way where every client is on their own /30 subnet, rather than having every client in the same /24 (or whatever) subnet.
So to answer your question, it is NOT possible to prevent client to client communication if they are on the same subnet using OpenVPN's server/client configuration alone.
With that said, of course you could use iptables to block specific traffic per host, however this would be quite cumbersome not only to configure, but also to scale. Therefore, your best option would be to configure /30 subnets for each client.
Yes. As mentioned in the manpage:
--client-to-client Because the OpenVPN server mode handles multiple clients through a single tun or tap interface, it is effectively a router. The --client-to-client flag tells OpenVPN to internally route client- to-client traffic rather than pushing all client-originating traffic to the TUN/TAP interface. When this option is used, each client will "see" the other clients which are currently connected. Otherwise, each client will only see the server. Don't use this option if you want to firewall tunnel traffic using custom, per-client rules.So, by removing this line from your configuration, you will restrict the clients to only talk to the server.
5